A few days ago a new political party emerged in India called ‘Cockroach Janata Party’ following remarks attributed to the Chief Justice of India during a court hearing and apparently rapidly gained traction online through memes. I am going to talk about the political aspect of it in a bit but first want to talk about the branding of the party. When a new party/organization is formed people try to get a brand image that points to what the party wants to do. For example, when AAP (Aam Aadmi Party) was formed they named themselves as the representing the regular man (Aam Admi) and their symbol was a Broom because they claimed to be looking at sweeping the corruption clean from the country (what they actually did is a whole other story).
This new party decided to call themselves Cockroach janata party. A cockroach is something that no sane person wants in their house, if you find one in a house you know that is is not cleaned properly. I don’t know anyone who would say something like ‘oh I want more Cockroach’s in my house’. So why would you choose an insect that pretty much every human would hate finding in their houses?
Cockroach’s breed in dirty houses with food left in the open or garbage not taken out regularly (found this out the hard way when I got an infestation in my house). Is the party saying that they want India (Bharat) to go back to the ‘good old days’ of corruption and dirty cities without public toilets? (India went from 38.70 per cent population having access to toilets in 2013 to 87.5% having access in 2025). There is a lot we need to improve but we have come a long way since 2014.
The founder of the party Abhijeet Dipke used to work with AAP Communications, doesn’t stay in India (He lives in Boston) claims that the name was chosen because of the quote by Chief Justice Surya Kant during a Supreme Court hearing where they supposedly called the youth of India cockroaches & parasites but claimed later that he was misquoted. (If that quote is accurate then action should be taken against him). Abhijeet on the other hand is known for his pro-Pakistan takes on Section 370 and during the CAA protests. Other folks pushing the party are similarly not in India and are happily staying Abroad but still push the anti-India narratives.
The ‘party’ claims to be a popular platform that is giving voice to GenZ concerns but if you look at the founders, the follower metrics and the actual real life impact/reach it doesn’t seem to be there. Most of the noise generated by the party is coming from the usual Anti-India groups followed by folks from Pakistan and Bangladesh. The ‘party’ appealed everyone to assemble in front of the Bangalore Town Hall and even with 20 million followers on Instagram & 200k followers on Twitter, exactly 0 people showed up for their protest. In contrast when Anna Hazare protested in Bangalore in 2011 with his India Against Corruption (IAC) movement over 87,000 people were there supporting him against the corruption we saw in India. (I was there in Bangalore at the time and saw the support they have).

Cockroach Janta Party has 20 million followers on Instagram.
CJP has 200k followers on Twitter.
They appealed to everyone to assemble in the front of Town hall Bengaluru.
The number of GenZ reached in the front of the Town Hall: 0
In the past few weeks, we have seen multiple attempts to malign India starting with the Norwegian journalist who claimed that Modi didn’t answer questions during a briefing but walked out when given the option to ask questions in an actual press conference. Then we have the whole drama being created about a casual mutually respectful joke between two leaders that are comfortable enough with each other to joke with each other. Look at the video below, does it look like any of the participants are disrespecting the other?:
Modi Gifts ‘Melody’ Toffee to Giorgia Meloni During High Stakes Italy Visit | ‘Melodi’ Diplomacy
In contrast, apparently Nehru lighting a cigarette for Mrs Simon and hugging/kissing foreign diplomats/heads of state is all ok and in the best of manners and diplomacy. I can only imagine the ruckus that would have been raised if Modi had kissed a foreign head of state or hugged them.

Nehru, Prime Minister of India lighting the cigarette for Mrs Simon, wife of Deputy High Commissioner of Britain, 1960.
After their miserable showing in West Bengal and barely adequate showing in Kerala & Tamil Nadu the opposition parties are at this point literally throwing things at BJP/Modi/India to see what sticks. The same person who is complaining today that India doesn’t have a good AI ecosystem when compared to China was protesting shirtless in the AI summit back in February.
This is the latest attempt by Congress, AAP and others to try to get GenZ to revolt against the government. Online followers & bots can be bought to create a buzz but the actual humans in India know what is what when they see this absolutely transparent attempt to hurt Bharat’s image on the international stage. Some more facts about about the claim that Modi is a Dictator are easily countered by facts comparing Congress actions and BJP actions.
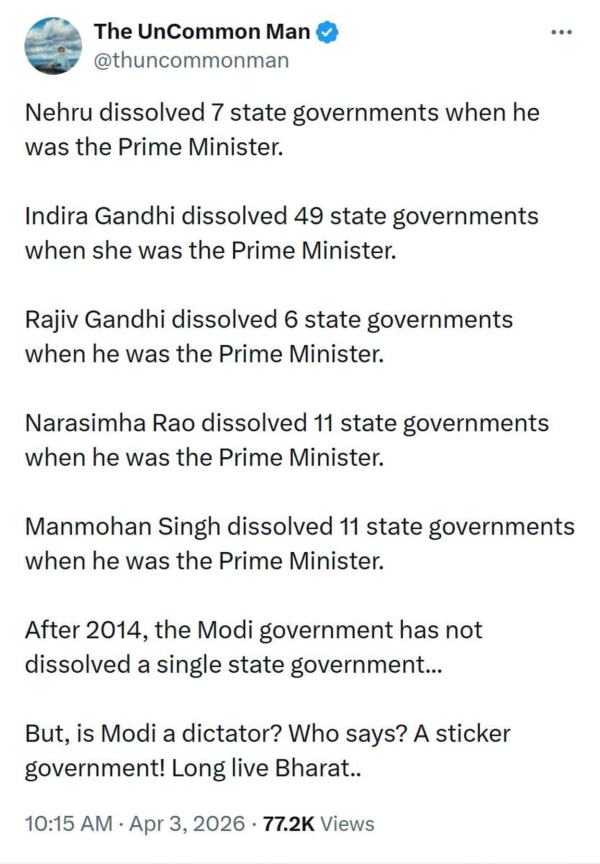
Nehru dissolved 7 state governments when he was the Prime Minister.
Indira Gandhi dissolved 49 state governments when she was the Prime Minister.
Rajiv Gandhi dissolved 6 state governments when he was the Prime Minister.
Narasimha Rao dissolved 11 state governments when he was the Prime Minister.
Manmohan Singh dissolved 11 state governments when he was the Prime Minister.
After 2014, the Modi government has not dissolved a single state government…
But, is Modi a dictator? Who says? A sticker government! Long live Bharat..
There are so many such examples that it would takes a series of posts to cover them all. But I will end this post with just a statement that BJP & Modi have a lot of room for improvements and I don’t always agree with their policies but when compared to the other parties such as TMC, Congress, AAP and others I will take BJP over them anytime. Atleast they are trying to improve the country (and in a few cases making themselves richer while at it) as opposed to the others who seem to be in it for just making themselves richer.
– Suramya