Yesterday Threads launched a beta version of their fediverse integration and that is actually a great thing. Users who have access can enable federation on their account and users on other Federated systems such as Mastodon can follow them, comment and like their posts as if they were directly on the Threads server. (Comments are not yet propagated back to Threads but is in the works).
First a bit of background information. Threads is a microblogging site similar to Twitter that was created by Meta to take advantage of the fact that Twitter was becoming more and more unusable. Fediverse is a ensemble of social networks which can communicate with each other, while remaining independent platforms. Basically it works similar to how email works, where I can have an account at suramya.com and still be able to communicate with someone who has an account at gmail.com. The system allows the individual servers / systems to communicate over the ActivityPub protocol, and anyone can implement it in their system. For example, my blog is connected to the Fediverse (Mastodon) and all posts here are automatically posted there. If I want I can enable more features here to allow me to browse/post posts across the various servers directly from my blog itself.
As you can imagine this is quite powerful and addresses the “Switching cost” which is an economists’ term for everything you have to give up when you change products or services. For social media networks the cost is that you will lose your connections on the network who don’t agree to shift with you and you loose access to the communities that are based in the network you want to leave. For example, a lot of Hobby networks, apartment groups etc are still on Facebook which means that I have to use FB if I want to keep myself up to date. A lot of government/company accounts are still on Twitter so I need to keep my account there if I want to connect with them or keep myself updated. Now imagine if that wasn’t the case. That is what federation means. People who want to use Threads can continue to use Threads and post over there and I would be able to follow them from my Mastodon account seamlessly and still interact with their posts.
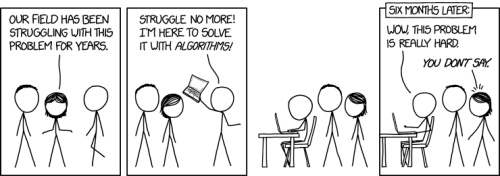
Unfortunately, as always there is a vocal minority who is raising a ruckus about this and are blocking them preemptively. These folks do raise some valid concerns such as posts on Mastodon servers will end up getting monetized and targeted for Ads, or the trolls from Meta services will start targeting folks on Mastodon servers or Fediverse will go the way of the XMPP (Extensible Messaging and Presence Protocol) that was adopted by Google and then slowly phased out/killed…
Lets talk about the last point first because it is a critical point. XMPP was a very promising protocol that was expected to allow users to chat with users of any chat service seamlessly. But it had a lot of issues some of which are discussed in the Hackernews Thread: Why XMPP failed and SMTP didn’t?. The highlights are:
- So multi device did not work: One device was designated “active” and would receive the messages, others would not.
- There was no history sync of any sort: If you had checked messages from home, they would not appear in your work computer’s history next morning. If you replied from home, you won’t be able to see your own messages at work PC.
- Anything mobile (mobile phone, laptop in coffee shops) was also unusable — you cannot start app and catch up on all missing messages. You had to be online to receive them.
These drawbacks (amongst others) did more to kill the protocol than anything Google did. The workarounds to resolve the issues listed above required a lot of custom hacks, kludges and prayers to get them to work and I talk about that from experience since I did setup and manage a XMPP server for a while.
Coming to the other points they are not a new concern that Threads is bringing in. We already have to worry about them in the existing ecosystem where we have servers that abuse the service and end up getting blocked. That is always an option where if they start doing things that we don’t like we can block them. Most posts on the Fediverse are already public by default so nothing is stopping Meta from consuming them to train their advertising system on it. The point about Trolls and Harassment campaigns doesn’t have an easy solution and for some servers that cater to marginalized communities blocking the entire Threads server might be a good idea.
Personally I like the approach Dansup from Pixelfed took, where they allow members, to block specific domains which blocks content and interactions from the domains the user chooses.
Having the ability to follow and interact with the formerly walled gardens from outside the garden is a good thing and we should build it up. Instead of dunking on it because it doesn’t do everything we want it to do. Lowering the Switching cost is a good thing longterm and we need more of this instead of ideological puritans jumping around about how the ‘impure’ masses from ‘the bad place’ are able to talk to and interact with folks in the ‘pure’ server defiling it’s ideological purity.
In a way it is a similar argument that we used to have about open source and closed source systems. Purists wanted everything from BIOS up to be Open Source and realistically speaking this is not possible. Users will want proprietary software because the open source ones are not up to the mark. As an example, I run MS Office on my Linux machine using Crossover because Libreoffice(or OpenOffice) still doesn’t have full compatibility. I did this after the nth time OpenOffice messed up the layout after I edited it using OO. Asking users to compromise on their work is not going to happen. They just want things to work and work seamlessly and having to account for compatibility issues or usability issues is a non-starter. Once a system is usable and reliable like Apache server or Linux folks will start using it as evidenced by a majority of the servers on the web running Open Source software. Till that happens we need to ensure we support workarounds and not look down on people using the workarounds.
Remember, perfection is the enemy of good enough as it prevents implementation of good improvements because they are not perfect.
– Suramya